Can Your Budget Handle Ransomware? Top 11 SLED Data Protection Challenges
Professionals in State, Local, and Educational (SLED) circles are in a tough spot. They’ve got to keep their data safe under a tight budget, battling against costly and stormy cyber threats. It’s a complex battlefield, no doubt. This post lists the 11 biggest challenges SLED organizations are facing right now when it comes to protecting their precious information. We’re talking about the must-tackle zones that need smart moves and sharp strategies to keep sensitive data under lock and key.
Top 11 SLED Data Protection Challenges
- Comprehensive Risk Assessment: Effective data protection starts with understanding the landscape of potential threats. SLED organizations must regularly perform risk assessments to identify vulnerabilities in their information systems.
These assessments should evaluate the susceptibility of data assets to cyber threats, physical damage, and human error. By pinpointing areas of weakness, SLED entities can prioritize security enhancements, tailor their cybersecurity strategies to address specific risks, and allocate resources more effectively.
This proactive approach ensures that protective measures are aligned with the actual risk profile, enhancing the overall security posture of the organization.
- Budget-Conscious Cybersecurity Solutions: Amid financial constraints, SLED entities must find cybersecurity solutions that are both effective and economical. By exploring cost-effective measures, organizations can achieve robust security against complex threats without exceeding budgetary limits.
These solutions should offer scalability and flexibility, allowing for the efficient allocation of resources in response to changing cybersecurity demands. Emphasizing the importance of strategic investment, SLED entities can enhance their cybersecurity posture through smart, budget-friendly choices, ensuring the protection of critical data and services against evolving digital threats.
- Encryption of Sensitive Data: Encryption transforms sensitive data into a coded format, making it inaccessible to unauthorized individuals. For SLED entities, encrypting data at rest (stored data) and in transit (data being transmitted) is crucial.
This ensures that personal information, financial records, and other confidential data are protected against unauthorized access and breaches. Encryption serves as a robust line of defense, safeguarding data even if physical security measures fail or if data is intercepted during transmission.
Implementing strong encryption standards is a key requirement for maintaining the confidentiality and integrity of sensitive information within SLED organizations.
- Multi-factor Authentication (MFA): MFA adds a critical security layer by requiring users to provide two or more verification factors to access data systems. This approach significantly reduces the risk of unauthorized access due to compromised credentials.
By combining something the user knows (like a password) with something the user has (such as a security token or a smartphone app confirmation), MFA ensures that stolen or guessed passwords alone are not enough to breach systems.
For SLED entities, implementing MFA is essential for protecting access to sensitive systems and data, particularly in an era of increasing phishing attacks and credential theft.
- Data Backup Regularity: Regular, scheduled backups are essential for ensuring data integrity and availability. SLED organizations must establish a stringent backup schedule that reflects the value and sensitivity of their data.
This involves determining which data sets are critical for operations and ensuring they are backed up frequently enough to minimize data loss in the event of a system failure, data corruption, or cyberattack. Regular backups, combined with comprehensive inventory and classification of data, ensure that all vital information is recoverable, supporting the continuity of operations and services.
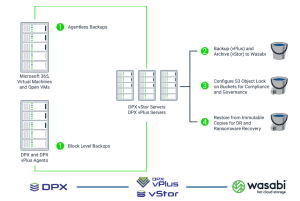
- Offsite and Immutable Backup Storage: Storing backups offsite and using immutable storage mediums protects against a range of threats, including natural disasters, physical damage, and ransomware attacks. Offsite storage ensures that a physical event (like a fire or flood) at the primary site does not compromise the ability to recover data.
Immutable storage prevents data from being altered or deleted once written, offering a safeguard against malicious attempts to compromise backup integrity. For SLED entities, these practices are integral to a resilient data protection strategy, ensuring data can be restored to maintain public service continuity.
- Testing and Validation of Backup Integrity: Regular testing of backups for integrity and restorability is crucial. This process verifies that data can be effectively restored from backups when necessary.
SLED organizations must implement procedures to periodically test backup solutions, ensuring that data is not only being backed up correctly but can also be restored in a timely and reliable manner.
This practice identifies potential issues with backup processes or media, allowing for corrective actions before an actual disaster occurs. It’s a critical step in ensuring the operational readiness of data recovery strategies.
- Data Minimization and Retention Policies: Data minimization and retention policies are about storing only what is necessary and for as long as it is needed. This approach reduces the volume of data vulnerable to cyber threats and aligns with privacy regulations that require the deletion of personal data once its purpose has been fulfilled.
SLED organizations should establish clear guidelines on data collection, storage, and deletion, ensuring unnecessary or outdated data is systematically purged. These policies help mitigate risks related to data breaches and ensure compliance with data protection laws, minimizing legal and reputational risks.
- Incident Response and Recovery Planning: An incident response plan outlines procedures for addressing data breaches, cyberattacks, or other security incidents. It includes identifying and responding to incidents, mitigating damages, and communicating with stakeholders.
Recovery planning focuses on restoring services and data after an incident. For SLED entities, having a well-defined, regularly tested incident response and recovery plan is vital. It ensures preparedness to act swiftly in the face of security incidents, minimizing impact and downtime, and facilitating a quicker return to normal operations.
- Compliance with Legal and Regulatory Requirements: SLED organizations are subject to a complex web of regulations concerning data protection and privacy. Compliance involves adhering to laws and regulations like FERPA for educational institutions, HIPAA for health-related entities, and various state data breach notification laws.
Ensuring compliance requires a thorough understanding of these regulations, implementing necessary controls, and regularly reviewing policies and procedures to accommodate changes in the law. This not only protects individuals’ privacy but also shields organizations from legal penalties and reputational damage.
- Employee Training and Awareness Programs: Human error remains a significant vulnerability in data protection. Training and awareness programs are crucial for educating employees about their roles in safeguarding data, recognizing phishing attempts, and following organizational policies and procedures.
Regular training ensures that staff are aware of the latest threats and best practices for data security. For SLED entities, fostering a culture of cybersecurity awareness can significantly reduce the risk of data breaches caused by insider threats or negligence, making it an essential component of any data protection strategy.
Facing these challenges highlights the urgent need for a smart plan that fixes today’s security problems and gets ready for tomorrow’s dangers. To tackle these big issues, a set of solutions is designed to close the gap between possible risks and the strong protections needed to stop them. These solutions show us how to go from spotting cybersecurity issues to putting strong safeguards in place. This shows a forward-thinking and thorough way to keep the digital and day-to-day operations of SLED organizations safe.
What Are the Solutions to the Top 11 Challenges Faced by SLED?
- Automated and Scheduled Backups: To ensure data is regularly backed up without relying on manual processes, which can lead to gaps in the backup schedule.
- Affordable and Flexible License: Emphasizes the need for cost-effective and adaptable licensing models that allow SLED entities to scale security services according to budget and needs, ensuring essential cybersecurity tools are accessible without financial strain.
- Encryption and Security: Strong encryption for data at rest and in transit, ensures that sensitive information remains secure from unauthorized access.
- Multi-Factor Authentication (MFA): Support for MFA to secure access to the backup software, reducing the risk of unauthorized access due to compromised credentials.
- Immutable Backup Options: The ability to create immutable backups that cannot be altered or deleted once they are written, protecting against ransomware and malicious attacks.
- Offsite and Cloud Backup Capabilities: Features that enable backups to be stored offsite or in the cloud, providing protection against physical disasters and enabling scalability.
- Integrity Checking and Validation: Tools for automatically verifying the integrity of backups to ensure they are complete and can be successfully restored when needed.
- Data Minimization and Retention Management: Capabilities for setting policies on data retention, ensuring that only necessary data is kept and that old data is securely deleted in compliance with policies and regulations.
- Incident Response Features: Integration with incident response tools and workflows, enabling quick action in the event of a data breach or loss scenario.
- Compliance Reporting and Audit Trails: Tools for generating reports and logs that demonstrate compliance with relevant regulations and policies, aiding in audit processes.
- User Training and Awareness Resources: Availability of resources or integrations with training platforms to educate users on best practices and threats, enhancing the overall security posture.
Key Takeaways
SLED organizations must urgently tackle data protection challenges as they protect sensitive information from growing cyber threats. This blog shows the complex task of keeping public sector data safe, emphasizing the need for encryption, regular backups, following the law, and teaching employees about cybersecurity.
Facing these challenges head-on requires not just understanding and diligence, but also the right partnership. Catalogic Software data protection experts are ready to bolster your cyber resilience. Our team specializes in empowering SLED IT managers with tailored solutions that address the unique threats and compliance requirements facing public sector organizations today.