Ensuring the Data Integrity of your Backups with GuardMode

The Case for Ensuring Data Integrity
While writing a long term paper, I accidentally overwrote and replaced a long passage with a single character – the unintended consequence of a Select All and an accidental keyboard press. I didn’t realize that a good portion of my paper was gone until I went back to proofread it, and I had to go back through multiple versions only to discover that the error had been saved in those versions as well. While it took me another couple of hours to rewrite the section, it taught a valuable of lesson in that just because you have a saved copy, the data contained within it may not be the data you expect or want.
Such is true in today’s environment where unscrupulous actors encrypt data for ransom and even your backup copies may not spare you from the fallout when those copies were affected with ransomware as well. Data protection has always been multi-faceted by concerns regarding recovery point objective (how often to backup, how long to retain the backup) and recovery time objective (how quick to recover in the event of data loss). There are very few solutions that look at the data integrity and data validity − is the data that is being restored the data that I want?
GuardMode is an add-on feature set to DPX that was built to address this concern and help ensure the data integrity of your backups.
What does GuardMode do?
DPX GuardMode actively monitors filesystem activity on the backup clients that you are protecting within DPX and identifies data that may have been compromised. From an architectural perspective, there is a GuardMode agent that needs to be installed on the client server that will be monitored.
As users interact with the filesystem on the server, the GuardMode agent will detect this activity and alert administrators on violations to configurable rulesets defined by the system administrator.
Early Detection Strategies
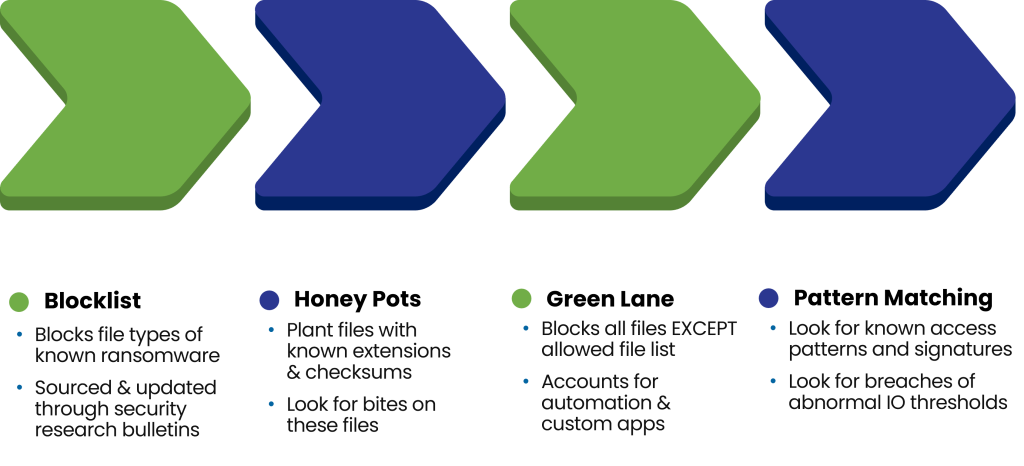
In addition to default behaviors that alert based on file properties like file entropy, the value associated with randomness of a file where higher entropy values could signify encrypted data. Backup admins are able to customize what they classify as violations via:
Blocklist– The blocklist is a list of file types/extensions that a user does not want on their filesystem. It can be automatically updated and populated directly from the Catalogic support webserver and exceptions can defined within the DPX user interface. By using a blocklist, administrators can receive alerts when these files (most of them are known ransomware file types) land on the filesystem.
Honey Pots – A honey pot is like a booby trap, put in place to alert an administrator when users are making modifications to a folder location that has been designated as a honey pot. When a file modification occurs to a honey pot, the trap is sprung and an administrator is notified that someone is making changes to files that should not change.
GuardMode Proactive Detection Strategies
Threshold Monitoring
Threshold violations occur when I/O operations exceed a limit. Users can configure these limits based on frequency, interval scanning, and other parameters that sum to a weighted value. For example, a server which typically doesn’t have much activity in terms of filesystem changes suddenly has over 100K file writes in 30 secs should raise an alarm that something outside of the ordinary is occurring. This type of monitoring can raise a flag and allow an administrator to investigate more deeply and follow-up with the appropriate user making those changes.
Restoring the Data You Need
Data protection is more than just backup and restore. It needs to be multi-faceted to address the many ways in which data can be backed up and how quickly that data can be restored and reused. DPX addressed these concerns by providing a block level incremental backup and a disk to disk to tape/cloud (3-2-1) backup strategy as well as multiple options for restoring data like Instant Access, Bare Metal Recovery, and Instant Virtualization. Now with GuardMode, DPX can help ensure the integrity of the data that is being protected so that the data you restore is the data you want.
Come check out some videos on the YouTube page for an overview and demonstration of GuardMode.
GuardMode is continually evolving and becoming even more tightly integrated with DPX. In the future, we will tie early detection and recovery capabilities even further by using analytics and metadata from GuardMode to help with guided restore capabilities in DPX. Then you too can hopefully avoid having to put on another pot of coffee at 2AM trying to finish a project due the next morning.

